5G New Radio (NR) Use Cases
- (5G Three Connectivity Types - IEEE Xplore)
- Overview
5G or New Radio (NR) is a next (fifth) generation of mobile networks after LTE (the forth generation). While next versions of LTE specifications are under development and there will be further LTE evolution, there is a new standard published that defines 5G.
During early days of LTE it was developed primary to provide subscribers with Mobile Broadband services (MBB) based on IP connectivity. Later LTE specifications were extended with new functionality to support another use cases as well. For example new functionality includes an ability to support a massive number of low cost devices for IoT (Internet of Things) use cases that have specific and different requirements comparing to initial MBB use cases.
- The 3GPP SMARTER Project
From a functional point of view, the most logical approach is to build a set of dedicated networks each adapted to serve one type of business customer. These dedicated networks would permit the implementation of tailor-made functionality and network operation specific to the needs of each business customer, rather than a one-size-fits-all approach as witnessed in the current and previous mobile generations which would not be economically viable.
These three primary 5G New Radio (NR) use cases are defined by the 3GPP as part of its SMARTER (Study on New Services and Markets Technology Enablers) project. The objective behind SMARTER was to develop high level use cases and identify what features and functionality 5G would need to deliver to enable them. It began in 2015 and resulted in over 70 use cases, initially grouped into five categories which has since been trimmed to three. They are characterised by the performance attributes the particular use cases will require, although there is some overlap.
- Three Primary 5G NR Use Cases
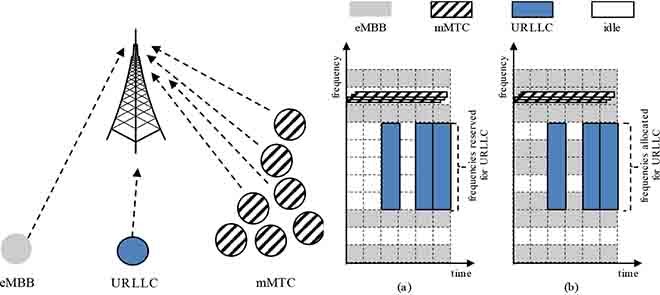
The three sets of primary 5G New Radio (NR) use cases are as follows:
- Enhanced Mobile Broadband (eMBB): data-driven use cases requiring high data rates across a wide coverage area.
- Ultra Reliable Low Latency Communications (URLLC): strict requirements on latency and reliability for mission critical communications, such as remote surgery, autonomous vehicles or the Tactile Internet.
- Massive Machine Type Communications (mMTC): need to support a very large number of devices in a small area, which may only send data sporadically, such as Internet of Things (IoT) use cases.
eMBB supports stable connections with very high peak data rates, as well as moderate rates for cell-edge users; mMTC supports a massive number of Internet of Things (IoT) devices, which are only sporadically active and send small data payloads; URLLC supports low-latency transmissions of small payloads with very high reliability from a limited set of terminals, which are active according to patterns typically specified by outside events, such as alarms.
- enhanced Mobile BroadBand (eMBB)
eMBB (enhanced Mobile BroadBand) is more or less straightforward evolution of mobile networks (as it was mentioned above MBB is an initial use case for LTE). 5G should push further network throughput and enhance user experience. For 5G target throughput is up to 20 Gbps in downlink channel (i.e. from a base station to user equipment). To meet this requirement new frequency bands are needed for 5G to form channel with bandwidth of up to 1 GHz. Another enablers of such high throughputs are multi-antenna transmission and beamforming. There are not so many free bands in low frequencies (<6 GHz) as most of bands are allocated already. So to have ultra wide channels 5G networks can be launched using millimeter waves (e.g. 28 GHz). In this range there are quite many free bands that can be allocated to provide mobile wireless services. While low frequencies (ideally <1 GHz) are used to provide appropriate network coverage.
Multi-antenna transmission is an important component of 5G network especially in high bands where waves propagation is very limited. Multi-antenna transmission improves network coverage and increases spectral efficiency.
- massive Machine-Type Communication (mMTC)
mMTC (massive Machine-Type Communication) is about a massive number of devices such as various sensors and meters, remote equipment monitoring and so on. Typically these devices are low cost (<5$). Another distinctive feature of such devices is very low energy consumption and relatively small amount of transmitted data. So high rates are not required for this use cases. While an ability to support a lot of devices that infrequently transmit small packets (usually delay tolerant) and effective UE (User Equipment) energy saving features are key building blocks in this area.
- Ultra-Reliable and Low-Latency Communication (URLLC)
URLLC (Ultra-Reliable and Low-Latency Communication) is partially (or even mostly) about machine-to-machine communication as well as the one above. But in contrast to the previous one this class is also about ultra low latency (<1 ms in one direction) and extremely high reliability. Examples that fall into this bucket are factory automation, traffic safety and Vehical to Everything (V2X), robots control and remote medicine and so on. To meet requirements raised by this class of use cases there is a specific set of 5G features specified. For example support of mini-slot that allows to transmit data within a part of slot (aka TTI in LTE). That reduces transmission time on radio link between gNB (base station) and UE (user equipment). Moreover in 5G there are much more strong requirements on data processing time in gNB and UE, i.e. allowed time to process data is much shorter (comparing to LTE).
[More to come ...]